Infrastructure
All terminals used by our customers communicate with our platform through a local area network (LAN) and through an Internet connection. This could be the customer’s office LAN and its office Internet connection. Or it could be the home WIFI and Internet connection. Same thing if the customer is staying at a hotel.
The infrastructure used by our customers is out of our scope and it is the responsibility of the customer (assisted by his/her IT partner) to deploy a VoIP-ready infrastructure.
Router/Firewall configuration
In order for our service to operate properly, it is mandatory that the router/firewall doesn’t block traffic to/from our service. In 95% of the cases, traffic will travel smoothly through the existing or the new router/firewall. But it may happen that the router/firewall blocks or modifies traffic which makes our service unusable.
No big worries though. Some basic reconfiguration of your firewall/router will solve this:
- Ask the person who manages your router/firewall to allow outgoing traffic to our IP ranges (for all ports and protocols). You’ll find the list of IPs in your admin portal, in “Config” > “Advanced” > “Account details” > “Infrastructure” tab.
- If the router/firewall supports QoS (Quality of Service), assign a higher priority to the traffic exchanged with our IP range.
- Some routers also include a feature called SIP ALG (http://en.wikipedia.org/wiki/Application-level_gateway). Our experience shows that SIP ALG is often poorly implemented on low-cost routers and that it is better to disable SIP ALG.
- Make sure that the default NAT session timeout is > 30 seconds
Architectures
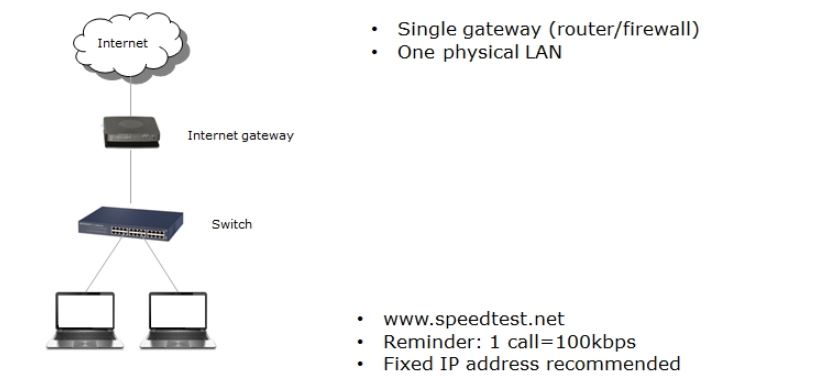
Below is the network architecture that most SMBs have deployed to handle their data network (no VoIP yet):
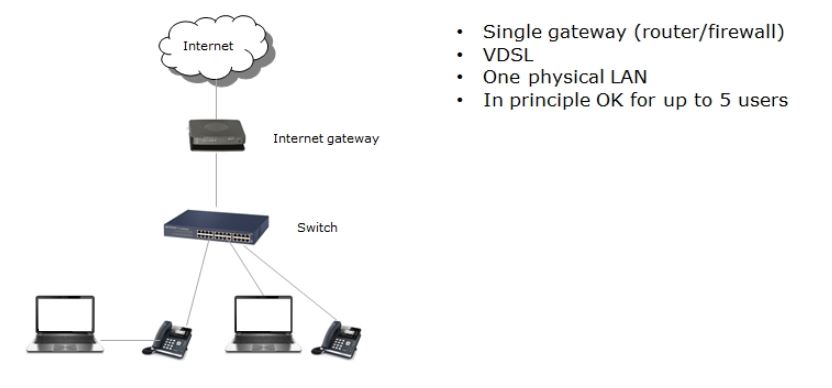
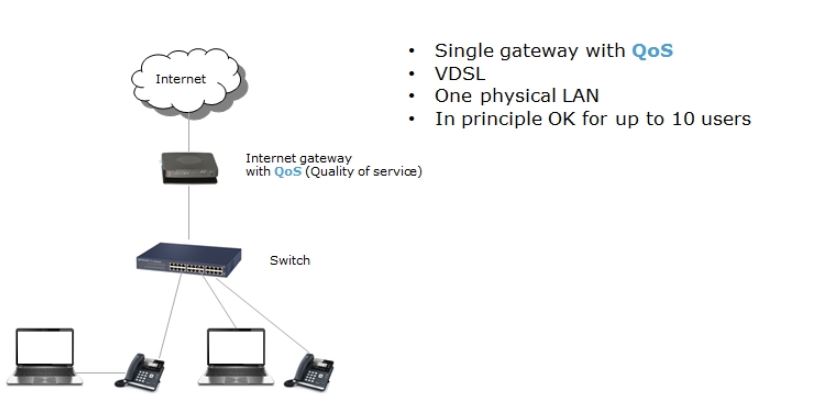
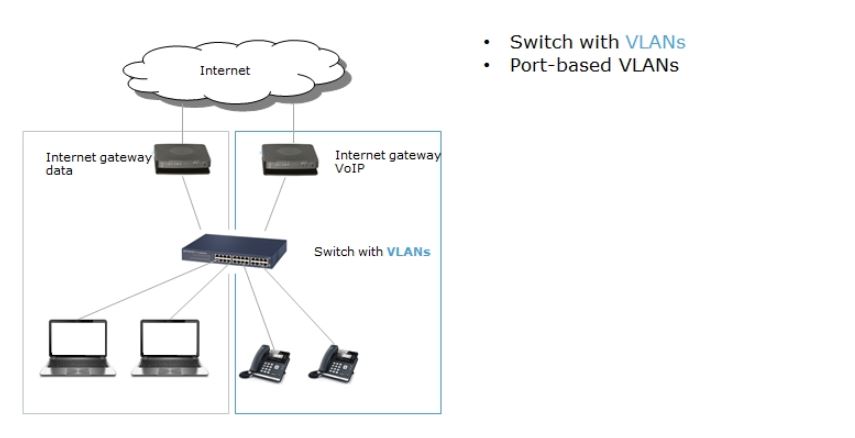
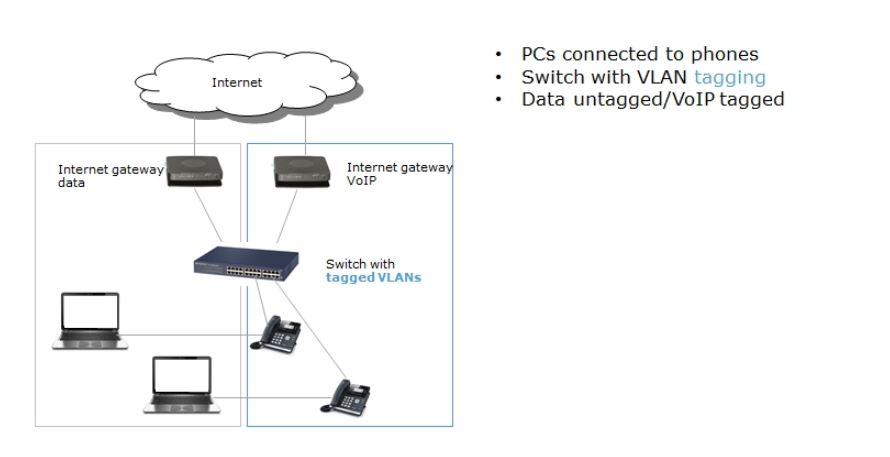
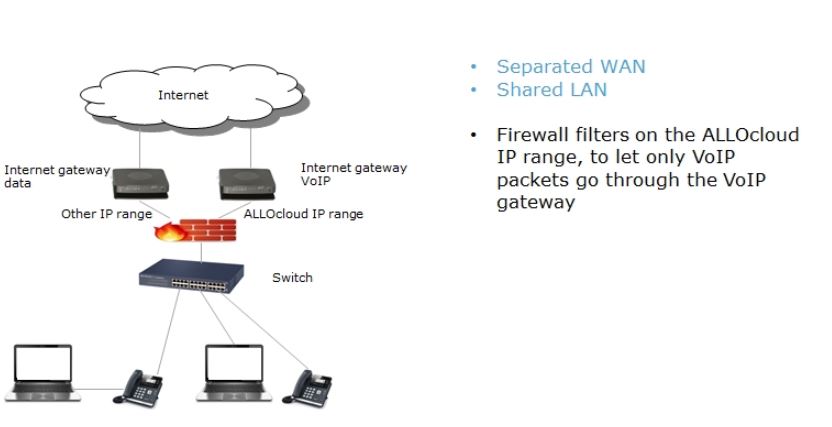
Below are the different network architectures that can be implemented in order to properly support IP telephony.